Trusted by teams at



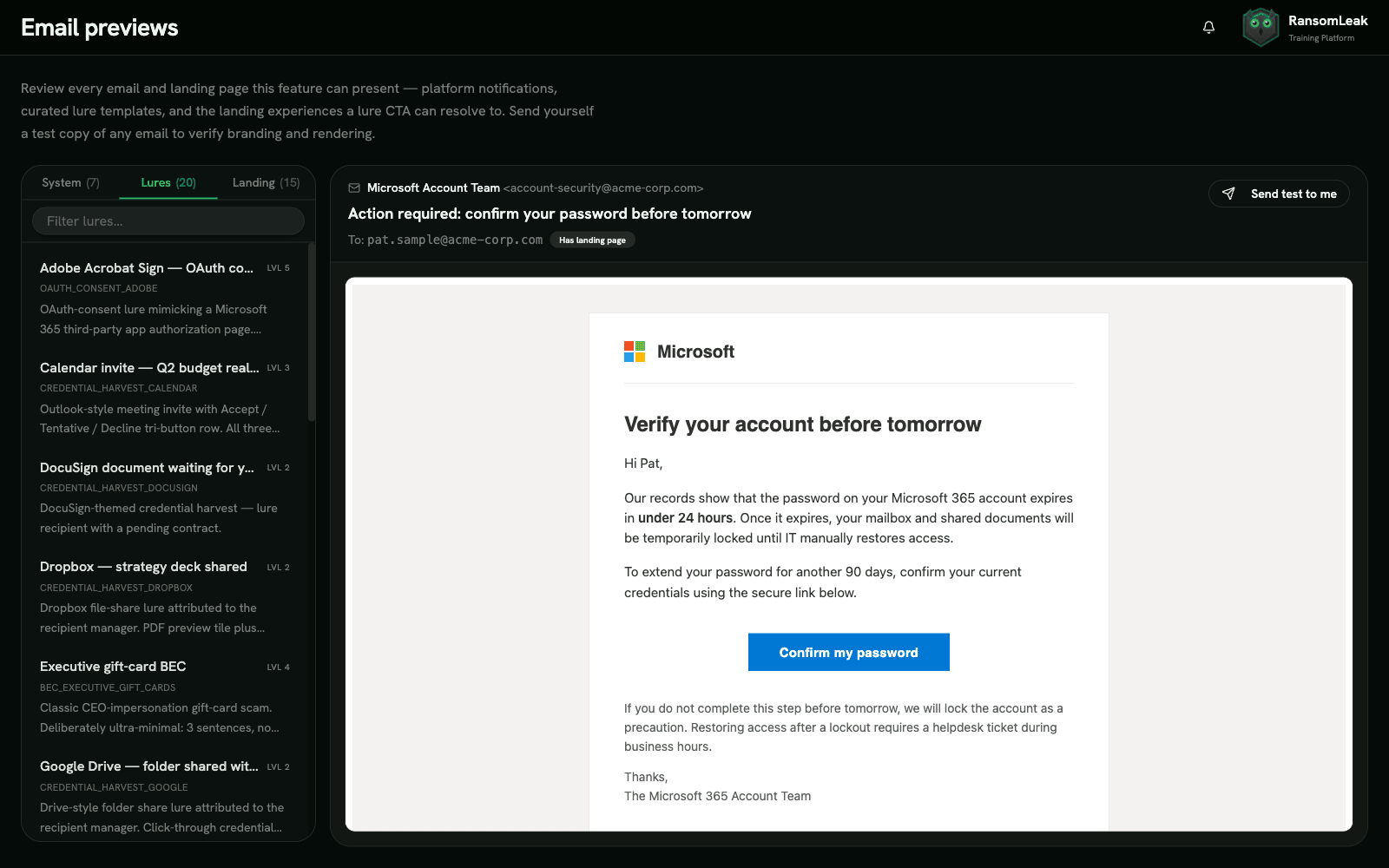
Phishing Simulations
Test your workforce against realistic phishing attacks delivered through direct mailbox injection. Track the full funnel from delivery to credential submission, and auto-assign targeted training to employees who click.
- M365 and Google Workspace direct injection bypasses spam filters
- Outlook and Gmail reporter buttons capture real-time employee reports
- Full-funnel analytics: delivered, opened, clicked, credentials, reported
- Auto-remediation assigns exercises to employees who fail simulations
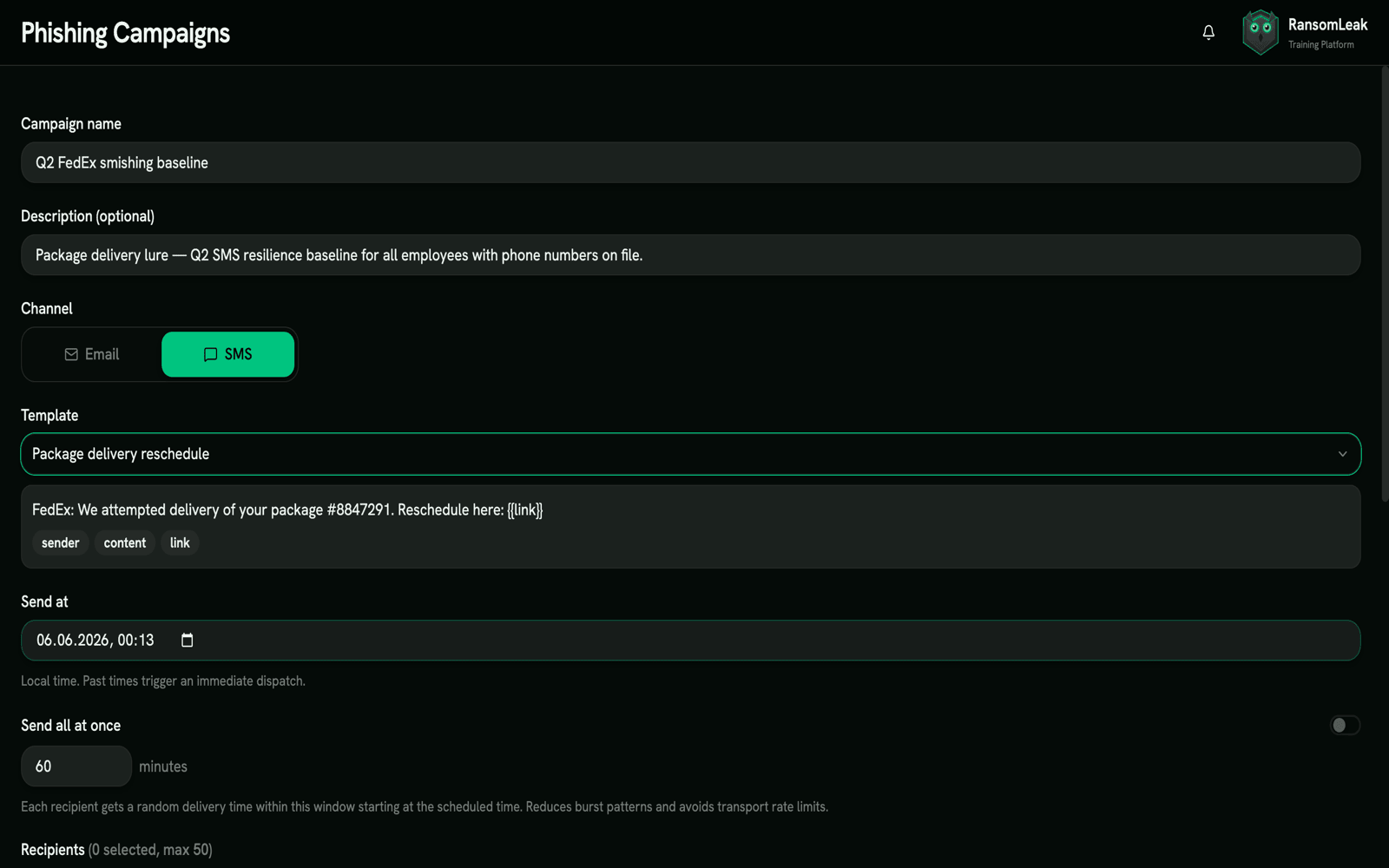
Smishing Simulations
Test your workforce against SMS phishing, the channel with no email gateway in front of it. Send realistic but harmless text lures over a real SMS transport, measure who taps and who reports, and route the rest into targeted training.
- Real SMS delivery gated to business hours and carrier rate limits
- Per-recipient tap and REPORT-reply tracking via signed, time-limited tokens
- Full-funnel analytics: sent, delivered, clicked, submitted, reported
- Auto-remediation enrolls anyone who taps the lure into targeted lessons
Latest blog articles
Practical guides on phishing, AI security, and awareness training. Written by the team behind the exercises.
Read all posts
AI Literacy Training: Meeting EU AI Act Article 4
EU AI Act Article 4 requires AI literacy for everyone who uses AI at work. See what the duty covers, who it reaches, and how to train staff to meet it.
Read the article
Deepfakes and the EU AI Act: Article 50 Transparency
The EU AI Act regulates deepfakes through Article 50 transparency duties. See what must be disclosed, who is responsible, and how to train teams to label synthetic media.
Read the article
EU AI Act and GDPR: Where the Two Laws Overlap
The EU AI Act and GDPR apply at the same time. See where the two laws overlap, where they differ, and how to train one team to satisfy both at once.
Read the article