Quishing (QR Code Phishing): How It Works and How to Stop It
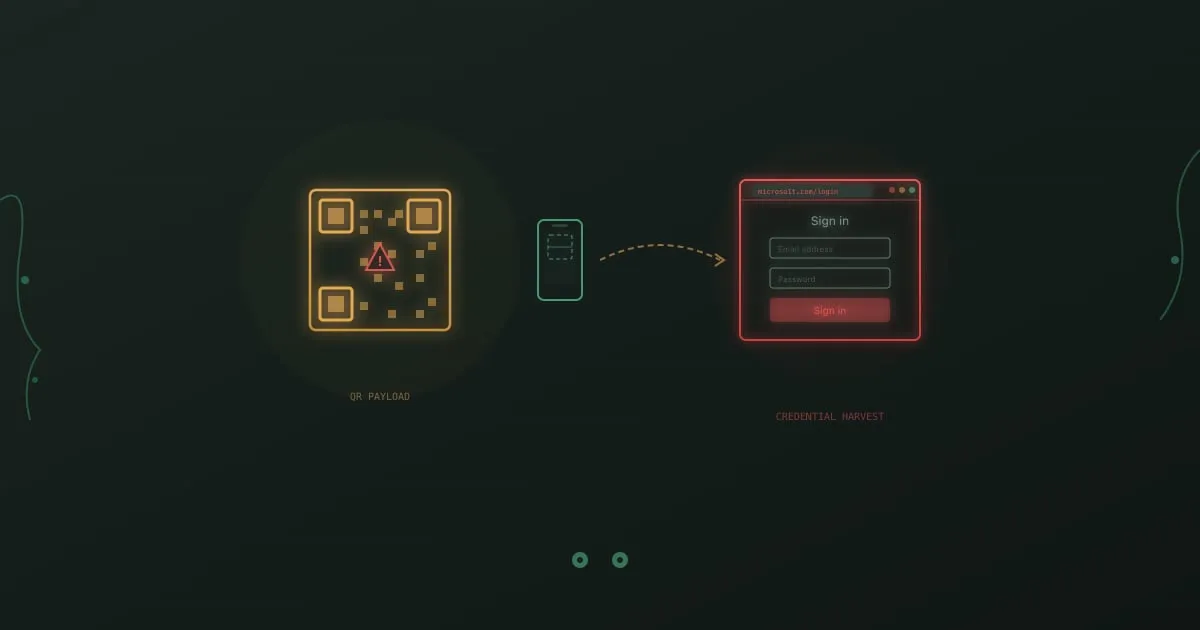
Quishing is phishing delivered through a QR code. The attacker encodes a malicious URL inside a square of pixels, drops it into a corporate email or prints it over a legitimate sign, and lets the target’s phone do the rest. Email filters see an image, not a link. The victim scans on a personal device that sits outside every corporate security control. That mismatch is what makes quishing work.