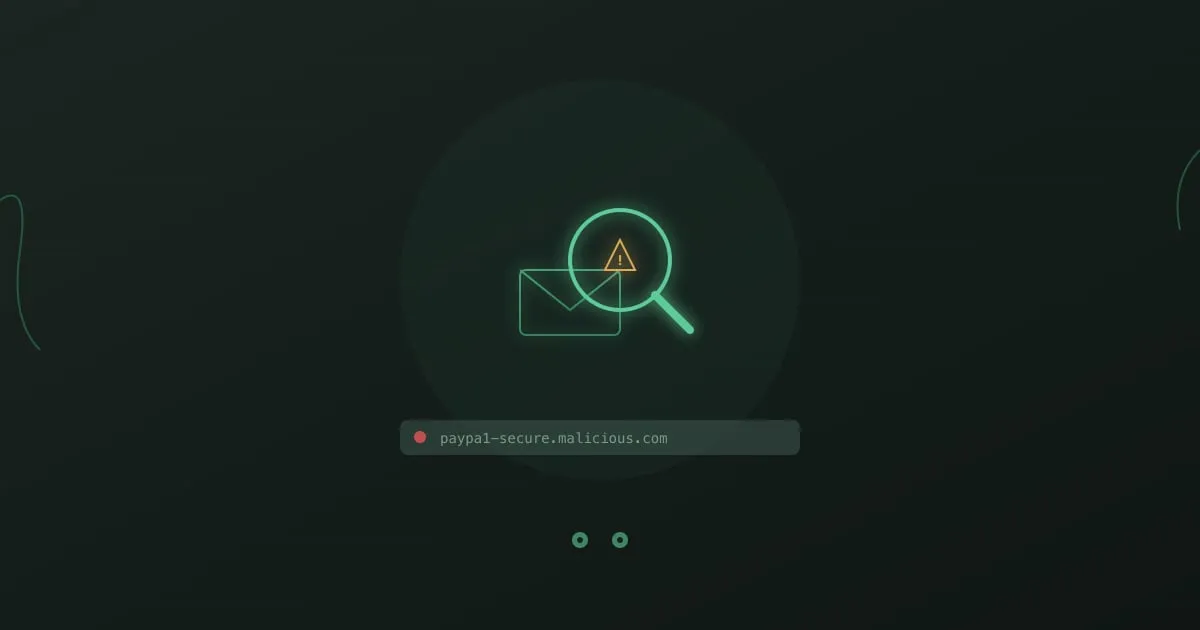
Type “gogle.com” into your browser. You misspelled it. Twenty years ago, that typo would have landed you on a page stuffed with ads. Today, it might land you on a pixel-perfect replica of Google’s login page, one that captures your username and password before redirecting you to the real thing. You would never know.
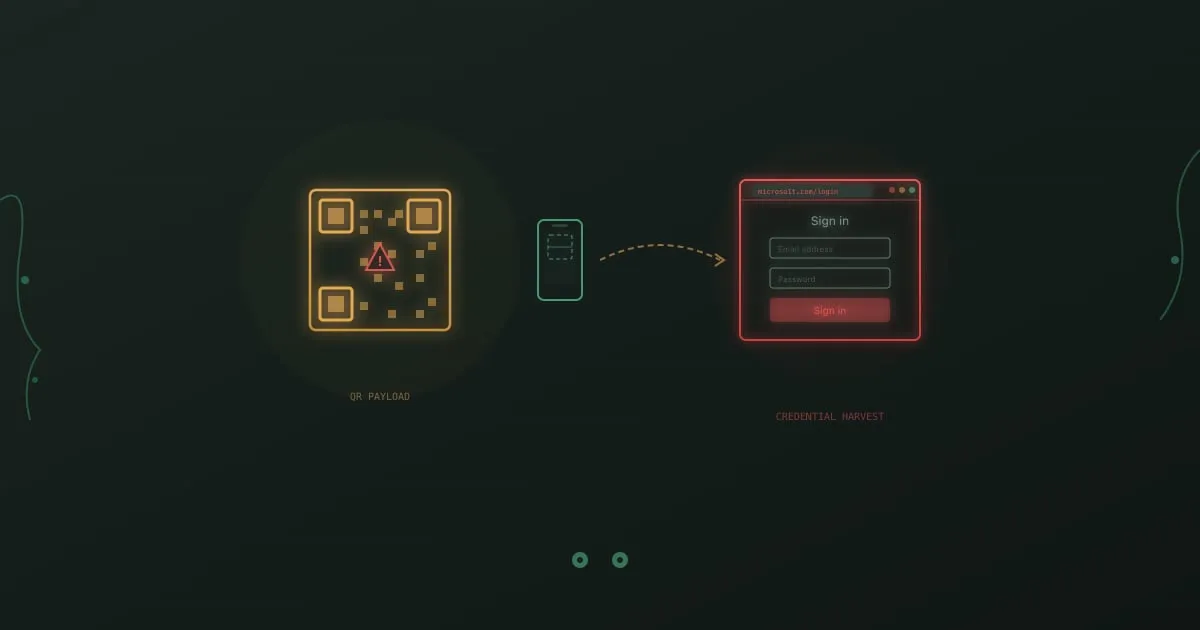
This is typosquatting, and it has been around since domain names became valuable. What changed is the sophistication. Modern typosquatting campaigns do not just buy obvious misspellings. They register domains using character substitutions that are nearly invisible to the human eye, pair them with valid HTTPS certificates, and deploy them as part of targeted credential-harvesting operations against specific companies.
Palo Alto Networks’ Unit 42 found that roughly 13,857 squatting domains were registered per month in 2023, with typosquatting and combosquatting accounting for the majority. These are not opportunistic parked pages. Many are active phishing sites with a shelf life measured in hours, just long enough to harvest a batch of credentials before being reported and taken down.